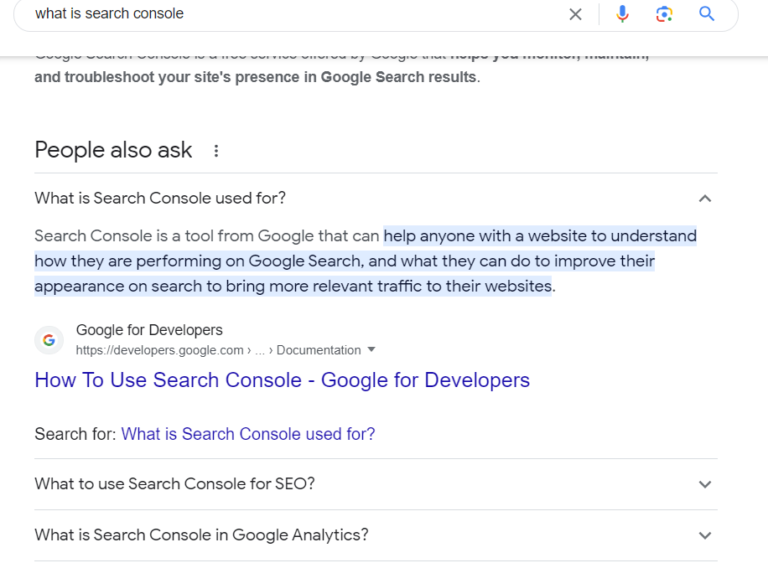
What is Risk in Cybersecurity
Risk in cybersecurity refers to the potential for harm or loss resulting from threats exploiting vulnerabilities in computer systems, networks, and data. In this comprehensive article, we’ll explore the concept of risk in cybersecurity, examine common threats and vulnerabilities, discuss the impact of cyber risks on organizations, and provide insights into mitigation strategies to safeguard against cyber threats.

Understanding Risk in Cybersecurity
Defining Cybersecurity Risk:
Cybersecurity risk encompasses the likelihood of a cyber threat exploiting vulnerabilities to compromise the confidentiality, integrity, or availability of information assets. It involves assessing the potential impact of threats and vulnerabilities on an organization’s operations, reputation, and financial well-being.
Components of Cyber Risk:
Cyber risk consists of several interconnected components:
- Threats: Malicious actors, such as hackers, cybercriminals, and nation-state actors, pose threats to organizations by exploiting vulnerabilities in technology, processes, or human behavior.
- Vulnerabilities: Weaknesses or gaps in security defenses, including software flaws, misconfigurations, outdated systems, and human error, create opportunities for threats to exploit and infiltrate systems.
- Impact: The consequences of a successful cyber attack, including data breaches, financial losses, operational disruptions, regulatory penalties, reputational damage, and legal liabilities, constitute the impact of cyber risk.
Common Threats and Vulnerabilities
Threat Landscape:
Cyber threats come in various forms, including:
- Malware: Malicious software, such as viruses, worms, trojans, ransomware, and spyware, designed to infiltrate systems, steal data, or disrupt operations.
- Phishing: Social engineering attacks that trick users into divulging sensitive information, such as passwords, credit card numbers, or personal data, through deceptive emails, websites, or messages.
- Denial of Service (DoS) Attacks: Attempts to overwhelm or disrupt computer systems, networks, or services by flooding them with excessive traffic or requests, rendering them unavailable to legitimate users.
Read more about DOS Attack here
Vulnerability Exploitation:
Common vulnerabilities exploited by cyber threats include:
- Unpatched Software: Failure to install security patches and updates leaves systems vulnerable to known vulnerabilities that attackers can exploit to gain unauthorized access or execute malicious code.
- Weak Authentication: Inadequate password policies, default credentials, and lack of multi-factor authentication increase the risk of unauthorized access to accounts and systems.
- Misconfigured Systems: Improperly configured servers, firewalls, routers, and other network devices may expose sensitive data or provide entry points for attackers to exploit.
Impact of Cyber Risks on Organizations
Business Consequences:
The consequences of cyber risks can be severe and far-reaching:
- Financial Losses: Data breaches, theft of intellectual property, and operational disruptions can result in significant financial losses, including direct costs, legal fees, regulatory fines, and remediation expenses.
- Reputational Damage: Breaches of customer trust, negative publicity, and loss of credibility can damage an organization’s reputation and erode customer confidence, leading to long-term consequences for brand value and market competitiveness.
- Operational Disruptions: Cyber attacks that disrupt critical business operations, such as manufacturing processes, supply chains, or online services, can cause downtime, productivity losses, and delays in service delivery.
Mitigation Strategies for Cyber Risks
Risk Management Approach:
Effective risk management involves:
- Risk Assessment: Identifying, assessing, and prioritizing cyber risks based on their likelihood and potential impact on business objectives.
- Risk Mitigation: Implementing controls, safeguards, and countermeasures to reduce the likelihood and impact of cyber threats, including technical controls, security policies, and employee training.
- Incident Response: Developing and implementing incident response plans and procedures to detect, contain, and recover from cyber attacks promptly.
Security Best Practices:
Key security measures to mitigate cyber risks include:
- Patch Management: Regularly applying security patches and updates to software, operating systems, and firmware to address known vulnerabilities and reduce the attack surface.
- Access Control: Implementing strong authentication mechanisms, least privilege access controls, and user account management practices to limit unauthorized access to sensitive data and systems.
- Network Segmentation: Segmenting networks, segregating sensitive assets, and implementing firewalls and intrusion detection systems to prevent lateral movement of attackers and limit the impact of breaches.
Conclusion
Risk in cybersecurity represents the potential for harm or loss resulting from threats exploiting vulnerabilities in information systems and networks. By understanding the components of cyber risk, recognizing common threats and vulnerabilities, and implementing effective mitigation strategies, organizations can enhance their security posture and minimize the impact of cyber attacks. With proactive risk management, continuous monitoring, and investment in cybersecurity controls and practices, businesses can mitigate the evolving threat landscape and protect their assets, reputation, and resilience in an increasingly digital world.
Also read: What Does a Cybersecurity Analyst Do